Security Cards
Method Overview
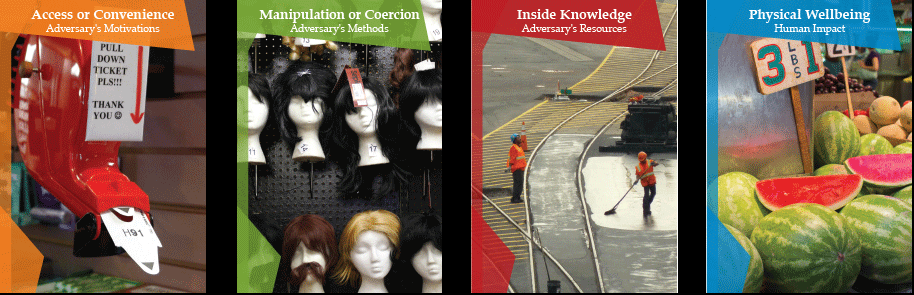
A set of ethical considerations presented as cards, designed for teams to consider the potential security threats and human impacts their products may have in order to avoid such negative consequences.
Getting Started
Materials: Set of Security Cards
Participants: Individual, Group
Steps (from the Security Cards website):
- Security Cards include 42 cards divided into 4 dimensions; Choose the dimension(s) that apply to your product or project.
- Use an indeterminate number of cards within that/those dimension(s) and consider how your own work relates to this context/concept.
- Implement your findings into your design approaches in order to avoid potential negative impacts and consequences.